| Name | cli-automation JSON |
| Version |
1.8.3
 JSON
JSON |
| download |
| home_page | None |
| Summary | Network Automation from the Command Line |
| upload_time | 2025-10-27 03:12:31 |
| maintainer | None |
| docs_url | None |
| author | Ed Scrimaglia |
| requires_python | <4.0,>=3.10 |
| license | GNU GENERAL PUBLIC LICENSE
Version 2, June 1991
Copyright (C) 1989, 1991 Free Software Foundation, Inc.,
51 Franklin Street, Fifth Floor, Boston, MA 02110-1301 USA
Everyone is permitted to copy and distribute verbatim copies
of this license document, but changing it is not allowed.
Preamble
The licenses for most software are designed to take away your
freedom to share and change it. By contrast, the GNU General Public
License is intended to guarantee your freedom to share and change free
software--to make sure the software is free for all its users. This
General Public License applies to most of the Free Software
Foundation's software and to any other program whose authors commit to
using it. (Some other Free Software Foundation software is covered by
the GNU Lesser General Public License instead.) You can apply it to
your programs, too.
When we speak of free software, we are referring to freedom, not
price. Our General Public Licenses are designed to make sure that you
have the freedom to distribute copies of free software (and charge for
this service if you wish), that you receive source code or can get it
if you want it, that you can change the software or use pieces of it
in new free programs; and that you know you can do these things.
To protect your rights, we need to make restrictions that forbid
anyone to deny you these rights or to ask you to surrender the rights.
These restrictions translate to certain responsibilities for you if you
distribute copies of the software, or if you modify it.
For example, if you distribute copies of such a program, whether
gratis or for a fee, you must give the recipients all the rights that
you have. You must make sure that they, too, receive or can get the
source code. And you must show them these terms so they know their
rights.
We protect your rights with two steps: (1) copyright the software, and
(2) offer you this license which gives you legal permission to copy,
distribute and/or modify the software.
Also, for each author's protection and ours, we want to make certain
that everyone understands that there is no warranty for this free
software. If the software is modified by someone else and passed on, we
want its recipients to know that what they have is not the original, so
that any problems introduced by others will not reflect on the original
authors' reputations.
Finally, any free program is threatened constantly by software
patents. We wish to avoid the danger that redistributors of a free
program will individually obtain patent licenses, in effect making the
program proprietary. To prevent this, we have made it clear that any
patent must be licensed for everyone's free use or not licensed at all.
The precise terms and conditions for copying, distribution and
modification follow.
GNU GENERAL PUBLIC LICENSE
TERMS AND CONDITIONS FOR COPYING, DISTRIBUTION AND MODIFICATION
0. This License applies to any program or other work which contains
a notice placed by the copyright holder saying it may be distributed
under the terms of this General Public License. The "Program", below,
refers to any such program or work, and a "work based on the Program"
means either the Program or any derivative work under copyright law:
that is to say, a work containing the Program or a portion of it,
either verbatim or with modifications and/or translated into another
language. (Hereinafter, translation is included without limitation in
the term "modification".) Each licensee is addressed as "you".
Activities other than copying, distribution and modification are not
covered by this License; they are outside its scope. The act of
running the Program is not restricted, and the output from the Program
is covered only if its contents constitute a work based on the
Program (independent of having been made by running the Program).
Whether that is true depends on what the Program does.
1. You may copy and distribute verbatim copies of the Program's
source code as you receive it, in any medium, provided that you
conspicuously and appropriately publish on each copy an appropriate
copyright notice and disclaimer of warranty; keep intact all the
notices that refer to this License and to the absence of any warranty;
and give any other recipients of the Program a copy of this License
along with the Program.
You may charge a fee for the physical act of transferring a copy, and
you may at your option offer warranty protection in exchange for a fee.
2. You may modify your copy or copies of the Program or any portion
of it, thus forming a work based on the Program, and copy and
distribute such modifications or work under the terms of Section 1
above, provided that you also meet all of these conditions:
a) You must cause the modified files to carry prominent notices
stating that you changed the files and the date of any change.
b) You must cause any work that you distribute or publish, that in
whole or in part contains or is derived from the Program or any
part thereof, to be licensed as a whole at no charge to all third
parties under the terms of this License.
c) If the modified program normally reads commands interactively
when run, you must cause it, when started running for such
interactive use in the most ordinary way, to print or display an
announcement including an appropriate copyright notice and a
notice that there is no warranty (or else, saying that you provide
a warranty) and that users may redistribute the program under
these conditions, and telling the user how to view a copy of this
License. (Exception: if the Program itself is interactive but
does not normally print such an announcement, your work based on
the Program is not required to print an announcement.)
These requirements apply to the modified work as a whole. If
identifiable sections of that work are not derived from the Program,
and can be reasonably considered independent and separate works in
themselves, then this License, and its terms, do not apply to those
sections when you distribute them as separate works. But when you
distribute the same sections as part of a whole which is a work based
on the Program, the distribution of the whole must be on the terms of
this License, whose permissions for other licensees extend to the
entire whole, and thus to each and every part regardless of who wrote it.
Thus, it is not the intent of this section to claim rights or contest
your rights to work written entirely by you; rather, the intent is to
exercise the right to control the distribution of derivative or
collective works based on the Program.
In addition, mere aggregation of another work not based on the Program
with the Program (or with a work based on the Program) on a volume of
a storage or distribution medium does not bring the other work under
the scope of this License.
3. You may copy and distribute the Program (or a work based on it,
under Section 2) in object code or executable form under the terms of
Sections 1 and 2 above provided that you also do one of the following:
a) Accompany it with the complete corresponding machine-readable
source code, which must be distributed under the terms of Sections
1 and 2 above on a medium customarily used for software interchange; or,
b) Accompany it with a written offer, valid for at least three
years, to give any third party, for a charge no more than your
cost of physically performing source distribution, a complete
machine-readable copy of the corresponding source code, to be
distributed under the terms of Sections 1 and 2 above on a medium
customarily used for software interchange; or,
c) Accompany it with the information you received as to the offer
to distribute corresponding source code. (This alternative is
allowed only for noncommercial distribution and only if you
received the program in object code or executable form with such
an offer, in accord with Subsection b above.)
The source code for a work means the preferred form of the work for
making modifications to it. For an executable work, complete source
code means all the source code for all modules it contains, plus any
associated interface definition files, plus the scripts used to
control compilation and installation of the executable. However, as a
special exception, the source code distributed need not include
anything that is normally distributed (in either source or binary
form) with the major components (compiler, kernel, and so on) of the
operating system on which the executable runs, unless that component
itself accompanies the executable.
If distribution of executable or object code is made by offering
access to copy from a designated place, then offering equivalent
access to copy the source code from the same place counts as
distribution of the source code, even though third parties are not
compelled to copy the source along with the object code.
4. You may not copy, modify, sublicense, or distribute the Program
except as expressly provided under this License. Any attempt
otherwise to copy, modify, sublicense or distribute the Program is
void, and will automatically terminate your rights under this License.
However, parties who have received copies, or rights, from you under
this License will not have their licenses terminated so long as such
parties remain in full compliance.
5. You are not required to accept this License, since you have not
signed it. However, nothing else grants you permission to modify or
distribute the Program or its derivative works. These actions are
prohibited by law if you do not accept this License. Therefore, by
modifying or distributing the Program (or any work based on the
Program), you indicate your acceptance of this License to do so, and
all its terms and conditions for copying, distributing or modifying
the Program or works based on it.
6. Each time you redistribute the Program (or any work based on the
Program), the recipient automatically receives a license from the
original licensor to copy, distribute or modify the Program subject to
these terms and conditions. You may not impose any further
restrictions on the recipients' exercise of the rights granted herein.
You are not responsible for enforcing compliance by third parties to
this License.
7. If, as a consequence of a court judgment or allegation of patent
infringement or for any other reason (not limited to patent issues),
conditions are imposed on you (whether by court order, agreement or
otherwise) that contradict the conditions of this License, they do not
excuse you from the conditions of this License. If you cannot
distribute so as to satisfy simultaneously your obligations under this
License and any other pertinent obligations, then as a consequence you
may not distribute the Program at all. For example, if a patent
license would not permit royalty-free redistribution of the Program by
all those who receive copies directly or indirectly through you, then
the only way you could satisfy both it and this License would be to
refrain entirely from distribution of the Program.
If any portion of this section is held invalid or unenforceable under
any particular circumstance, the balance of the section is intended to
apply and the section as a whole is intended to apply in other
circumstances.
It is not the purpose of this section to induce you to infringe any
patents or other property right claims or to contest validity of any
such claims; this section has the sole purpose of protecting the
integrity of the free software distribution system, which is
implemented by public license practices. Many people have made
generous contributions to the wide range of software distributed
through that system in reliance on consistent application of that
system; it is up to the author/donor to decide if he or she is willing
to distribute software through any other system and a licensee cannot
impose that choice.
This section is intended to make thoroughly clear what is believed to
be a consequence of the rest of this License.
8. If the distribution and/or use of the Program is restricted in
certain countries either by patents or by copyrighted interfaces, the
original copyright holder who places the Program under this License
may add an explicit geographical distribution limitation excluding
those countries, so that distribution is permitted only in or among
countries not thus excluded. In such case, this License incorporates
the limitation as if written in the body of this License.
9. The Free Software Foundation may publish revised and/or new versions
of the General Public License from time to time. Such new versions will
be similar in spirit to the present version, but may differ in detail to
address new problems or concerns.
Each version is given a distinguishing version number. If the Program
specifies a version number of this License which applies to it and "any
later version", you have the option of following the terms and conditions
either of that version or of any later version published by the Free
Software Foundation. If the Program does not specify a version number of
this License, you may choose any version ever published by the Free Software
Foundation.
10. If you wish to incorporate parts of the Program into other free
programs whose distribution conditions are different, write to the author
to ask for permission. For software which is copyrighted by the Free
Software Foundation, write to the Free Software Foundation; we sometimes
make exceptions for this. Our decision will be guided by the two goals
of preserving the free status of all derivatives of our free software and
of promoting the sharing and reuse of software generally.
NO WARRANTY
11. BECAUSE THE PROGRAM IS LICENSED FREE OF CHARGE, THERE IS NO WARRANTY
FOR THE PROGRAM, TO THE EXTENT PERMITTED BY APPLICABLE LAW. EXCEPT WHEN
OTHERWISE STATED IN WRITING THE COPYRIGHT HOLDERS AND/OR OTHER PARTIES
PROVIDE THE PROGRAM "AS IS" WITHOUT WARRANTY OF ANY KIND, EITHER EXPRESSED
OR IMPLIED, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF
MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE. THE ENTIRE RISK AS
TO THE QUALITY AND PERFORMANCE OF THE PROGRAM IS WITH YOU. SHOULD THE
PROGRAM PROVE DEFECTIVE, YOU ASSUME THE COST OF ALL NECESSARY SERVICING,
REPAIR OR CORRECTION.
12. IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR AGREED TO IN WRITING
WILL ANY COPYRIGHT HOLDER, OR ANY OTHER PARTY WHO MAY MODIFY AND/OR
REDISTRIBUTE THE PROGRAM AS PERMITTED ABOVE, BE LIABLE TO YOU FOR DAMAGES,
INCLUDING ANY GENERAL, SPECIAL, INCIDENTAL OR CONSEQUENTIAL DAMAGES ARISING
OUT OF THE USE OR INABILITY TO USE THE PROGRAM (INCLUDING BUT NOT LIMITED
TO LOSS OF DATA OR DATA BEING RENDERED INACCURATE OR LOSSES SUSTAINED BY
YOU OR THIRD PARTIES OR A FAILURE OF THE PROGRAM TO OPERATE WITH ANY OTHER
PROGRAMS), EVEN IF SUCH HOLDER OR OTHER PARTY HAS BEEN ADVISED OF THE
POSSIBILITY OF SUCH DAMAGES.
END OF TERMS AND CONDITIONS
How to Apply These Terms to Your New Programs
If you develop a new program, and you want it to be of the greatest
possible use to the public, the best way to achieve this is to make it
free software which everyone can redistribute and change under these terms.
To do so, attach the following notices to the program. It is safest
to attach them to the start of each source file to most effectively
convey the exclusion of warranty; and each file should have at least
the "copyright" line and a pointer to where the full notice is found.
<one line to give the program's name and a brief idea of what it does.>
Copyright (C) <year> <name of author>
This program is free software; you can redistribute it and/or modify
it under the terms of the GNU General Public License as published by
the Free Software Foundation; either version 2 of the License, or
(at your option) any later version.
This program is distributed in the hope that it will be useful,
but WITHOUT ANY WARRANTY; without even the implied warranty of
MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the
GNU General Public License for more details.
You should have received a copy of the GNU General Public License along
with this program; if not, write to the Free Software Foundation, Inc.,
51 Franklin Street, Fifth Floor, Boston, MA 02110-1301 USA.
Also add information on how to contact you by electronic and paper mail.
If the program is interactive, make it output a short notice like this
when it starts in an interactive mode:
Gnomovision version 69, Copyright (C) year name of author
Gnomovision comes with ABSOLUTELY NO WARRANTY; for details type `show w'.
This is free software, and you are welcome to redistribute it
under certain conditions; type `show c' for details.
The hypothetical commands `show w' and `show c' should show the appropriate
parts of the General Public License. Of course, the commands you use may
be called something other than `show w' and `show c'; they could even be
mouse-clicks or menu items--whatever suits your program.
You should also get your employer (if you work as a programmer) or your
school, if any, to sign a "copyright disclaimer" for the program, if
necessary. Here is a sample; alter the names:
Yoyodyne, Inc., hereby disclaims all copyright interest in the program
`Gnomovision' (which makes passes at compilers) written by James Hacker.
<signature of Ty Coon>, 1 April 1989
Ty Coon, President of Vice
This General Public License does not permit incorporating your program into
proprietary programs. If your program is a subroutine library, you may
consider it more useful to permit linking proprietary applications with the
library. If this is what you want to do, use the GNU Lesser General
Public License instead of this License.
|
| keywords |
networking
automation
typer
cli
python
|
| VCS |
|
| bugtrack_url |
|
| requirements |
No requirements were recorded.
|
| Travis-CI |
No Travis.
|
| coveralls test coverage |
No coveralls.
|
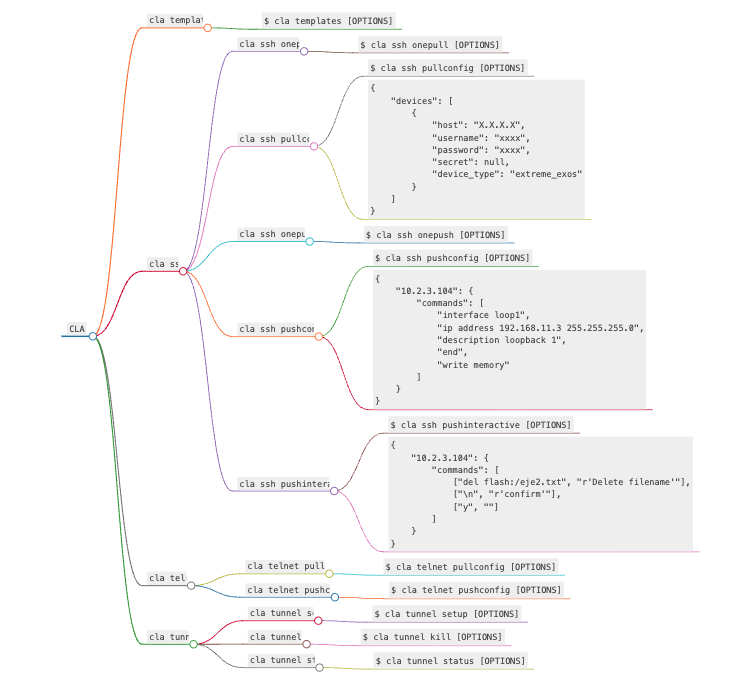
# `CLA`
[](https://pypi.org/project/cli-automation/)
[](https://pepy.tech/projects/cli-automation)
[](https://pypi.org/project/cli-automation/)
The CLA `Command Line interface Automation` is an Async Typer Python-based application designed to automate infrastructure directly from the command line. With CLA,
there is no need to write a single line of code, users simply follow the options presented in the help menu. When I thought about building CLA, I considered those
network engineers who have not yet acquired the necessary software knowledge, so `CLA was specifically designed to enable engineers who have not yet acquired software
knowledge to progress in the practice of automation`. CLA lets you both extract configurations and set up networking devices. You can enter
connection and configuration parameters either via the command line or using JSON files. Another reason I decided to develop CLA is to enable its commands to be invoked
from any programming language, once again, without requiring a single line of code for automation. CLA version 1.X.X focuses exclusively on Network Automation, while version
2.X.X will introduce Cloud Automation capabilities.
**Supported devices**:
- Cisco IOS
- Cisco XR
- Cisco XE
- Cisco NXOS
- Juniper
- Arista
- Huawei
- Extreme
- Alcatel
- Vyos
- Generic Telnet
**Instalation**:
Since CLA generates working files, it is recommended to create a virtual environment (to avoid potential conflicts between Python libraries) and install it there. Alternatively, if you prefer a global installation, you only need to create a working directory. Once installed, it is advisable to run the `cla --install-completion` command so that the TAB key helps navigate the options menu.
Additionally, while typing a command, the --help parameter can be used anywhere to obtain context-based assistance.
```
From PyPY:
$ pip install cli-automation
```
[`Project Repository`](https://github.com/escrimaglia/cli-automation)
**Usage**:
[`CLA Video Tutorial`](https://youtu.be/a51ng5ZVLD4?si=V2otTcLzNRwabBxj)
```console
$ cla [OPTIONS] COMMAND [ARGS]...
```
**Options**:
* `-V, --version`
* `--install-completion`: install completion for the current shell.
* `--show-completion`: show completion for the current shell, to copy it or customize the installation.
* `--help`: show this message and exit.
**Commands**:
* `templates`: Create examples of configuration files
* `logs`: Read logs file
* `ssh`: Accesses devices via the SSH protocol
* `telnet`: Accesses devices via the Telnet protocol
* `tunnel`: Manage tunnel with Bastion Host
## `cla templates`
The cla templates command generates example files, which can be used to create working files, both
for connection parameters and for device configuration commands
**Usage**:
```console
$ cla templates [OPTIONS]
```
**Options**:
* `-v, --verbose`: verbose level [default: 1; 0<=x<=2]
* `--help`: show this message and exit.
## `cla ssh`
The cla ssh command allows access to devices via the SSH protocol. The command can be used to pull or push configurations to devices.
To structure the output data when retrieving configurations, the `cla ssh pullconfig` command uses TextFSM templates. If the query
command is included in the templates, the output will be in JSON format; otherwise, the output will be in TXT format. The `cla ssh interactive`
command allows automating interactive CLI workflows which are often challenging. Confirmations, prompts, and unexpected inputs can easily break a script.
**Usage**:
```console
$ cla ssh [OPTIONS] COMMAND [ARGS]...
```
**Options**:
* `--help`: Show this message and exit.
**Commands**:
* `onepull`: Pull config from a single host
* `pullconfig`: Pull config from multiple hosts
* `onepush`: Push config to a single host
* `pushconfig`: Push config to multiple hosts
* `pushinteractive`: Push interactive commands to single/multiple hosts
### `cla ssh onepull`
Pull config from a single host
**Usage**:
```console
$ cla ssh onepull [OPTIONS]
```
**Options**:
* `-h, --host TEXT`: host name or ip address [required]
* `-u, --user TEXT`: username [required]
* `-c, --cmd Multiple -c parameter`: commands to execute on the device [required]
* `-t, --type [cisco_ios|cisco_xr|cisco_xe|cisco_nxos|juniper|juniper_junos|arista_eos|huawei|huawei_vrp|alcatel_sros|vyos|vyatta_vyos|extreme_exos|extreme]`: device type [required]
* `-p, --port INTEGER`: port [default: 22]
* `-v, --verbose`: verbose level [default: 0; 0<=x<=2]
* `-o, --output FILENAME Json file`: output file [default: output.json]
* `-d, --delay FLOAT RANGE`: global delay [default: 0.1; 0.1<=x<=4]
* `-s, --cfg TEXT`: ssh config file
* `--help`: Show this message and exit.
### `cla ssh pullconfig`
the commands can be entered via the command line or through a JSON file
**Usage**:
```console
$ cla ssh pullconfig [OPTIONS]
```
**Options**:
* `-h, --hosts FILENAME Json file`: group of hosts [required]
* `-c, --cmd Multiple -c parameter`: commands to execute on the device. Overrides FILENAME Json file
* `-f, --cmdf FILENAME Json file`: commands to execute on the device
* `-v, --verbose`: verbose level [default: 0; 0<=x<=2]
* `-o, --output FILENAME Json file`: output file [default: output.json]
* `--help`: show this message and exit.
```Example hosts json file:
{
"devices": [
{
"host": "X.X.X.X",
"username": "xxxx",
"password": "xxxx",
"secret": null,
"device_type": "extreme_exos"
}
]
}
```
### `cla ssh onepush`
the commands can be entered via the command line or through a JSON file
**Usage**:
```console
$ cla ssh onepush [OPTIONS]
```
**Options**:
* `-h, --host TEXT`: host name or ip address [required]
* `-u, --user TEXT`: username [required]
* `-t, --type [cisco_ios|cisco_xr|cisco_xe|cisco_nxos|juniper|juniper_junos|arista_eos|huawei|huawei_vrp|alcatel_sros|vyos|vyatta_vyos|extreme_exos|extreme]`: device type [required]
* `-c, --cmd Multiple -c parameter`: commands to configure the device. Overrides FILENAME Json file
* `-f, --cmdf FILENAME Json file`: commands to configure the device
* `-p, --port INTEGER`: port [default: 22]
* `-v, --verbose`: verbose level [default: 0; 0<=x<=2]
* `-o, --output FILENAME Json file`: output file [default: output.json]
* `-d, --delay FLOAT RANGE`: global delay factor [default: 0.1; 0.1<=x<=4]
* `-s, --cfg TEXT`: ssh config file
* `--help`: show this message and exit.
### `cla ssh pushconfig`
the commands must be provided through a JSON file
**Usage**:
```console
$ cla ssh pushconfig [OPTIONS]
```
**Options**:
* `-h, --hosts FILENAME Json file`: group of hosts [required]
* `-f, --cmd FILENAME Json file`: commands to configure the device [required]
* `-v, --verbose`: verbose level [default: 0; 0<=x<=2]
* `-o, --output FILENAME Json file`: output file [default: output.json]
* `--help`: show this message and exit.
```Example of cmd json file:
{
"10.2.3.104": {
"commands": [
"interface loop1",
"ip address 192.168.11.3 255.255.255.0",
"description loopback 1",
"end",
"write memory"
]
}
}
```
### `cla ssh pushinteractive`
Automating interactive CLI workflows is often challenging — confirmations, prompts, and unexpected inputs can easily break a script.
The commands and patterns must be provided through a cmd JSON file
**Usage**:
```console
$ cla ssh pushinteractive [OPTIONS]
```
**Options**:
* `-h, --hosts FILENAME Json file`: group of hosts [required]
* `-f, --cmd FILENAME Json file`: commands and patterns to execute on the device [required]
* `-v, --verbose`: verbose level [default: 0; 0<=x<=2]
* `-o, --output FILENAME Json file`: output file [default: output.json]
* `--help`: show this message and exit.
```Example of cmd json file:
{
"10.2.3.104": {
"commands": [
["del flash:/file2.txt", "Delete filename"],
["\n", "confirm"],
["y", ""]
]
}
}
```
## `cla telnet`
Telnet was added to CLA to access older devices that, for some reason, do not support SSH. Telnet operates in a generic way,
and configuration commands must follow the structure explained in the `telnet_commands_structure.json file`, file generated by the `cla templates` command.
However, whenever possible, SSH remains the preferred protocol.
**Usage**:
```console
$ cla telnet [OPTIONS] COMMAND [ARGS]...
```
**Options**:
* `--help`: show this message and exit.
**Commands**:
* `pullconfig`: Pull config from multiple hosts
* `pushconfig`: Push config file to multiple hosts
### `cla telnet pullconfig`
Pull config from multiple hosts
**Usage**:
```console
$ cla telnet pullconfig [OPTIONS]
```
**Options**:
* `-h, --hosts FILENAME Json file`: group of hosts [required]
* `-c, --cmd Single -c parameter`: command to execute on the device [required]
* `-v, --verbose`: verbose level [default: 0; 0<=x<=2]
* `-o, --output FILENAME text file`: output file [default: output.txt]
* `--help`: show this message and exit.
### `cla telnet pushconfig`
Push config file to multiple hosts
**Usage**:
```console
$ cla telnet pushconfig [OPTIONS]
```
**Options**:
* `-h, --hosts FILENAME Json file`: group of hosts [required]
* `-f, --cmdf FILENAME Json file`: commands to configure on the device [required]
* `-v, --verbose`: verbose level [default: 0; 0<=x<=2]
* `-o, --output FILENAME text file`: output file [default: output.txt]
* `--help`: show this message and exit.
## `cla tunnel`
Sometimes, the machine running CLA doesn’t have direct access to the devices and must go through a Bastion Host or Jump Host. To connect via a Bastion Host,
you can either configure SSH specifically or set up a tunnel (CLA supports both modes of operation). Personally, I think creating a tunnel is more efficient since it avoids SSH configuration,
specially when using `Telnet` commands.
Using `cla tunnel`, you can create or remove a SOCKS5 tunnel. For `cla tunnel` to function properly, the host running CLA must have easy access to the
Bastion Host (it should be listed in the Bastion Host's known_hosts file). CLA constantly monitors the tunnel’s status, but you can also manually check it using
the Linux command `lsof -i:{local_port}`.
**Usage**:
```console
$ cla tunnel [OPTIONS] COMMAND [ARGS]...
```
**Options**:
* `--help`: show this message and exit.
**Commands**:
* `setup`: Setup a tunnel to the Bastion Host
* `kill`: Kill the tunnel to the bastion Host
* `status`: Check the tunnel status
### `cla tunnel setup`
**Usage**:
```console
$ cla tunnel setup [OPTIONS]
```
**Options**:
* `-u, --user TEXT`: bastion host username [required]
* `-b, --bastion TEXT`: bastion name or ip address [required]
* `-p, --port INTEGER RANGE`: local port [default: 1080; 1000<=x<=1100]
* `-t, --timeout INTEGER RANGE`: timeout in seconds for the tunnel startup [default: 10; 3<=x<=25]
* `-v, --verbose`: verbose level [default: 1; 0<=x<=2]
* `--help`: show this message and exit.
### `cla tunnel kill`
**Usage**:
```console
$ cla tunnel kill [OPTIONS]
```
**Options**:
* `-v, --verbose`: verbose level [default: 1; 0<=x<=2]
* `--help`: show this message and exit.
### `cla tunnel status`
**Usage**:
```console
$ cla tunnel status [OPTIONS]
```
**Options**:
* `-p, --port INTEGER RANGE`: local port [default: 1080; 1000<=x<=1100]
* `-t, --timeout INTEGER RANGE`: timeout in seconds for the tunnel return its status [default: 10; 3<=x<=20]
* `-r, --test INTEGER`: remote port for testing the tunnel [default: 22]
* `-v, --verbose`: verbose level [default: 1; 0<=x<=2]
* `--help`: show this message and exit.
**Logging**:
CLA includes an efficient Log System that allows you to view INFO, DEBUG, CRITICAL, and ERROR details for each operation performed by CLA. The Log System includes a log file rotation based on file size. Each time the log file exceeds 5 MB, a new log file will be created.
Raw data
{
"_id": null,
"home_page": null,
"name": "cli-automation",
"maintainer": null,
"docs_url": null,
"requires_python": "<4.0,>=3.10",
"maintainer_email": null,
"keywords": "networking, automation, typer, cli, python",
"author": "Ed Scrimaglia",
"author_email": "edgardo.scrimaglia@gmail.com",
"download_url": "https://files.pythonhosted.org/packages/a9/69/86c7820d7e96494e0af23e3df57b9801833f313e4947dd4fddaaa2da933a/cli_automation-1.8.3.tar.gz",
"platform": null,
"description": "# `CLA`\n\n[](https://pypi.org/project/cli-automation/)\n[](https://pepy.tech/projects/cli-automation)\n[](https://pypi.org/project/cli-automation/)\n\nThe CLA `Command Line interface Automation` is an Async Typer Python-based application designed to automate infrastructure directly from the command line. With CLA,\nthere is no need to write a single line of code, users simply follow the options presented in the help menu. When I thought about building CLA, I considered those\nnetwork engineers who have not yet acquired the necessary software knowledge, so `CLA was specifically designed to enable engineers who have not yet acquired software \nknowledge to progress in the practice of automation`. CLA lets you both extract configurations and set up networking devices. You can enter \nconnection and configuration parameters either via the command line or using JSON files. Another reason I decided to develop CLA is to enable its commands to be invoked \nfrom any programming language, once again, without requiring a single line of code for automation. CLA version 1.X.X focuses exclusively on Network Automation, while version \n2.X.X will introduce Cloud Automation capabilities.\n\n**Supported devices**:\n\n- Cisco IOS\n- Cisco XR\n- Cisco XE\n- Cisco NXOS\n- Juniper\n- Arista\n- Huawei\n- Extreme\n- Alcatel\n- Vyos\n- Generic Telnet\n\n**Instalation**:\n\nSince CLA generates working files, it is recommended to create a virtual environment (to avoid potential conflicts between Python libraries) and install it there. Alternatively, if you prefer a global installation, you only need to create a working directory. Once installed, it is advisable to run the `cla --install-completion` command so that the TAB key helps navigate the options menu.\nAdditionally, while typing a command, the --help parameter can be used anywhere to obtain context-based assistance.\n\n```\nFrom PyPY:\n\n$ pip install cli-automation\n```\n\n[`Project Repository`](https://github.com/escrimaglia/cli-automation)\n\n**Usage**:\n\n[`CLA Video Tutorial`](https://youtu.be/a51ng5ZVLD4?si=V2otTcLzNRwabBxj)\n\n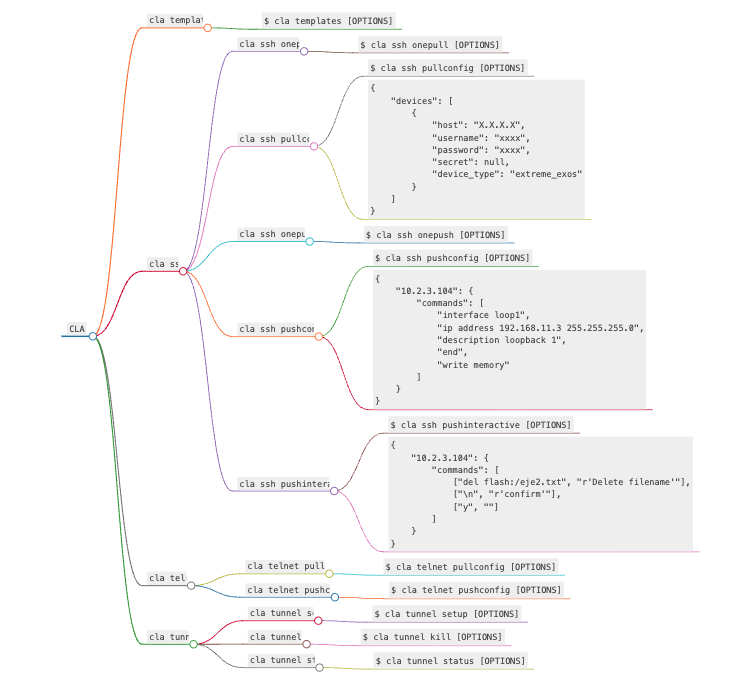\n\n\n```console\n$ cla [OPTIONS] COMMAND [ARGS]...\n```\n\n**Options**:\n\n* `-V, --version`\n* `--install-completion`: install completion for the current shell.\n* `--show-completion`: show completion for the current shell, to copy it or customize the installation.\n* `--help`: show this message and exit.\n\n**Commands**:\n\n* `templates`: Create examples of configuration files\n* `logs`: Read logs file\n* `ssh`: Accesses devices via the SSH protocol\n* `telnet`: Accesses devices via the Telnet protocol\n* `tunnel`: Manage tunnel with Bastion Host\n\n## `cla templates`\n\nThe cla templates command generates example files, which can be used to create working files, both \nfor connection parameters and for device configuration commands\n\n**Usage**:\n\n```console\n$ cla templates [OPTIONS]\n```\n\n**Options**:\n\n* `-v, --verbose`: verbose level [default: 1; 0<=x<=2]\n* `--help`: show this message and exit.\n\n## `cla ssh`\n\nThe cla ssh command allows access to devices via the SSH protocol. The command can be used to pull or push configurations to devices.\nTo structure the output data when retrieving configurations, the `cla ssh pullconfig` command uses TextFSM templates. If the query\ncommand is included in the templates, the output will be in JSON format; otherwise, the output will be in TXT format. The `cla ssh interactive` \ncommand allows automating interactive CLI workflows which are often challenging. Confirmations, prompts, and unexpected inputs can easily break a script.\n\n**Usage**:\n\n```console\n$ cla ssh [OPTIONS] COMMAND [ARGS]...\n```\n\n**Options**:\n\n* `--help`: Show this message and exit.\n\n**Commands**:\n\n* `onepull`: Pull config from a single host\n* `pullconfig`: Pull config from multiple hosts\n* `onepush`: Push config to a single host\n* `pushconfig`: Push config to multiple hosts\n* `pushinteractive`: Push interactive commands to single/multiple hosts\n\n### `cla ssh onepull`\n\nPull config from a single host\n\n**Usage**:\n\n```console\n$ cla ssh onepull [OPTIONS]\n```\n\n**Options**:\n\n* `-h, --host TEXT`: host name or ip address [required]\n* `-u, --user TEXT`: username [required]\n* `-c, --cmd Multiple -c parameter`: commands to execute on the device [required]\n* `-t, --type [cisco_ios|cisco_xr|cisco_xe|cisco_nxos|juniper|juniper_junos|arista_eos|huawei|huawei_vrp|alcatel_sros|vyos|vyatta_vyos|extreme_exos|extreme]`: device type [required]\n* `-p, --port INTEGER`: port [default: 22]\n* `-v, --verbose`: verbose level [default: 0; 0<=x<=2]\n* `-o, --output FILENAME Json file`: output file [default: output.json]\n* `-d, --delay FLOAT RANGE`: global delay [default: 0.1; 0.1<=x<=4]\n* `-s, --cfg TEXT`: ssh config file\n* `--help`: Show this message and exit.\n\n### `cla ssh pullconfig`\n\nthe commands can be entered via the command line or through a JSON file\n\n**Usage**:\n\n```console\n$ cla ssh pullconfig [OPTIONS]\n```\n\n**Options**:\n\n* `-h, --hosts FILENAME Json file`: group of hosts [required]\n* `-c, --cmd Multiple -c parameter`: commands to execute on the device. Overrides FILENAME Json file\n* `-f, --cmdf FILENAME Json file`: commands to execute on the device\n* `-v, --verbose`: verbose level [default: 0; 0<=x<=2]\n* `-o, --output FILENAME Json file`: output file [default: output.json]\n* `--help`: show this message and exit.\n\n```Example hosts json file:\n{\n \"devices\": [\n {\n \"host\": \"X.X.X.X\",\n \"username\": \"xxxx\",\n \"password\": \"xxxx\",\n \"secret\": null,\n \"device_type\": \"extreme_exos\"\n }\n ]\n}\n```\n\n### `cla ssh onepush`\n\nthe commands can be entered via the command line or through a JSON file\n\n**Usage**:\n\n```console\n$ cla ssh onepush [OPTIONS]\n```\n\n**Options**:\n\n* `-h, --host TEXT`: host name or ip address [required]\n* `-u, --user TEXT`: username [required]\n* `-t, --type [cisco_ios|cisco_xr|cisco_xe|cisco_nxos|juniper|juniper_junos|arista_eos|huawei|huawei_vrp|alcatel_sros|vyos|vyatta_vyos|extreme_exos|extreme]`: device type [required]\n* `-c, --cmd Multiple -c parameter`: commands to configure the device. Overrides FILENAME Json file\n* `-f, --cmdf FILENAME Json file`: commands to configure the device\n* `-p, --port INTEGER`: port [default: 22]\n* `-v, --verbose`: verbose level [default: 0; 0<=x<=2]\n* `-o, --output FILENAME Json file`: output file [default: output.json]\n* `-d, --delay FLOAT RANGE`: global delay factor [default: 0.1; 0.1<=x<=4]\n* `-s, --cfg TEXT`: ssh config file\n* `--help`: show this message and exit.\n\n### `cla ssh pushconfig`\n\nthe commands must be provided through a JSON file\n\n**Usage**:\n\n```console\n$ cla ssh pushconfig [OPTIONS]\n```\n\n**Options**:\n\n* `-h, --hosts FILENAME Json file`: group of hosts [required]\n* `-f, --cmd FILENAME Json file`: commands to configure the device [required]\n* `-v, --verbose`: verbose level [default: 0; 0<=x<=2]\n* `-o, --output FILENAME Json file`: output file [default: output.json]\n* `--help`: show this message and exit.\n\n```Example of cmd json file:\n{\n \"10.2.3.104\": {\n \"commands\": [\n \"interface loop1\",\n \"ip address 192.168.11.3 255.255.255.0\",\n \"description loopback 1\",\n \"end\",\n \"write memory\"\n ]\n }\n}\n```\n\n### `cla ssh pushinteractive`\n\nAutomating interactive CLI workflows is often challenging \u2014 confirmations, prompts, and unexpected inputs can easily break a script.\nThe commands and patterns must be provided through a cmd JSON file\n\n**Usage**:\n\n```console\n$ cla ssh pushinteractive [OPTIONS]\n```\n\n**Options**:\n\n* `-h, --hosts FILENAME Json file`: group of hosts [required]\n* `-f, --cmd FILENAME Json file`: commands and patterns to execute on the device [required]\n* `-v, --verbose`: verbose level [default: 0; 0<=x<=2]\n* `-o, --output FILENAME Json file`: output file [default: output.json]\n* `--help`: show this message and exit.\n\n```Example of cmd json file:\n{\n \"10.2.3.104\": {\n \"commands\": [\n [\"del flash:/file2.txt\", \"Delete filename\"],\n [\"\\n\", \"confirm\"],\n [\"y\", \"\"]\n ]\n }\n}\n```\n\n## `cla telnet`\n\nTelnet was added to CLA to access older devices that, for some reason, do not support SSH. Telnet operates in a generic way,\n and configuration commands must follow the structure explained in the `telnet_commands_structure.json file`, file generated by the `cla templates` command. \nHowever, whenever possible, SSH remains the preferred protocol.\n\n**Usage**:\n\n```console\n$ cla telnet [OPTIONS] COMMAND [ARGS]...\n```\n\n**Options**:\n\n* `--help`: show this message and exit.\n\n**Commands**:\n\n* `pullconfig`: Pull config from multiple hosts\n* `pushconfig`: Push config file to multiple hosts\n\n### `cla telnet pullconfig`\n\nPull config from multiple hosts\n\n**Usage**:\n\n```console\n$ cla telnet pullconfig [OPTIONS]\n```\n\n**Options**:\n\n* `-h, --hosts FILENAME Json file`: group of hosts [required]\n* `-c, --cmd Single -c parameter`: command to execute on the device [required]\n* `-v, --verbose`: verbose level [default: 0; 0<=x<=2]\n* `-o, --output FILENAME text file`: output file [default: output.txt]\n* `--help`: show this message and exit.\n\n### `cla telnet pushconfig`\n\nPush config file to multiple hosts\n\n**Usage**:\n\n```console\n$ cla telnet pushconfig [OPTIONS]\n```\n\n**Options**:\n\n* `-h, --hosts FILENAME Json file`: group of hosts [required]\n* `-f, --cmdf FILENAME Json file`: commands to configure on the device [required]\n* `-v, --verbose`: verbose level [default: 0; 0<=x<=2]\n* `-o, --output FILENAME text file`: output file [default: output.txt]\n* `--help`: show this message and exit.\n\n## `cla tunnel`\n\nSometimes, the machine running CLA doesn\u2019t have direct access to the devices and must go through a Bastion Host or Jump Host. To connect via a Bastion Host, \nyou can either configure SSH specifically or set up a tunnel (CLA supports both modes of operation). Personally, I think creating a tunnel is more efficient since it avoids SSH configuration, \nspecially when using `Telnet` commands. \nUsing `cla tunnel`, you can create or remove a SOCKS5 tunnel. For `cla tunnel` to function properly, the host running CLA must have easy access to the \nBastion Host (it should be listed in the Bastion Host's known_hosts file). CLA constantly monitors the tunnel\u2019s status, but you can also manually check it using \nthe Linux command `lsof -i:{local_port}`.\n\n**Usage**:\n\n```console\n$ cla tunnel [OPTIONS] COMMAND [ARGS]...\n```\n\n**Options**:\n\n* `--help`: show this message and exit.\n\n**Commands**:\n\n* `setup`: Setup a tunnel to the Bastion Host\n* `kill`: Kill the tunnel to the bastion Host\n* `status`: Check the tunnel status\n\n### `cla tunnel setup`\n\n**Usage**:\n\n```console\n$ cla tunnel setup [OPTIONS]\n```\n\n**Options**:\n\n* `-u, --user TEXT`: bastion host username [required]\n* `-b, --bastion TEXT`: bastion name or ip address [required]\n* `-p, --port INTEGER RANGE`: local port [default: 1080; 1000<=x<=1100]\n* `-t, --timeout INTEGER RANGE`: timeout in seconds for the tunnel startup [default: 10; 3<=x<=25]\n* `-v, --verbose`: verbose level [default: 1; 0<=x<=2]\n* `--help`: show this message and exit.\n\n### `cla tunnel kill`\n\n**Usage**:\n\n```console\n$ cla tunnel kill [OPTIONS]\n```\n\n**Options**:\n\n* `-v, --verbose`: verbose level [default: 1; 0<=x<=2]\n* `--help`: show this message and exit.\n\n### `cla tunnel status`\n\n**Usage**:\n\n```console\n$ cla tunnel status [OPTIONS]\n```\n\n**Options**:\n\n* `-p, --port INTEGER RANGE`: local port [default: 1080; 1000<=x<=1100]\n* `-t, --timeout INTEGER RANGE`: timeout in seconds for the tunnel return its status [default: 10; 3<=x<=20]\n* `-r, --test INTEGER`: remote port for testing the tunnel [default: 22]\n* `-v, --verbose`: verbose level [default: 1; 0<=x<=2]\n* `--help`: show this message and exit.\n\n**Logging**:\n\nCLA includes an efficient Log System that allows you to view INFO, DEBUG, CRITICAL, and ERROR details for each operation performed by CLA. The Log System includes a log file rotation based on file size. Each time the log file exceeds 5 MB, a new log file will be created.\n",
"bugtrack_url": null,
"license": " GNU GENERAL PUBLIC LICENSE\n Version 2, June 1991\n\n Copyright (C) 1989, 1991 Free Software Foundation, Inc.,\n 51 Franklin Street, Fifth Floor, Boston, MA 02110-1301 USA\n Everyone is permitted to copy and distribute verbatim copies\n of this license document, but changing it is not allowed.\n\n Preamble\n\n The licenses for most software are designed to take away your\nfreedom to share and change it. By contrast, the GNU General Public\nLicense is intended to guarantee your freedom to share and change free\nsoftware--to make sure the software is free for all its users. This\nGeneral Public License applies to most of the Free Software\nFoundation's software and to any other program whose authors commit to\nusing it. (Some other Free Software Foundation software is covered by\nthe GNU Lesser General Public License instead.) You can apply it to\nyour programs, too.\n\n When we speak of free software, we are referring to freedom, not\nprice. Our General Public Licenses are designed to make sure that you\nhave the freedom to distribute copies of free software (and charge for\nthis service if you wish), that you receive source code or can get it\nif you want it, that you can change the software or use pieces of it\nin new free programs; and that you know you can do these things.\n\n To protect your rights, we need to make restrictions that forbid\nanyone to deny you these rights or to ask you to surrender the rights.\nThese restrictions translate to certain responsibilities for you if you\ndistribute copies of the software, or if you modify it.\n\n For example, if you distribute copies of such a program, whether\ngratis or for a fee, you must give the recipients all the rights that\nyou have. You must make sure that they, too, receive or can get the\nsource code. And you must show them these terms so they know their\nrights.\n\n We protect your rights with two steps: (1) copyright the software, and\n(2) offer you this license which gives you legal permission to copy,\ndistribute and/or modify the software.\n\n Also, for each author's protection and ours, we want to make certain\nthat everyone understands that there is no warranty for this free\nsoftware. If the software is modified by someone else and passed on, we\nwant its recipients to know that what they have is not the original, so\nthat any problems introduced by others will not reflect on the original\nauthors' reputations.\n\n Finally, any free program is threatened constantly by software\npatents. We wish to avoid the danger that redistributors of a free\nprogram will individually obtain patent licenses, in effect making the\nprogram proprietary. To prevent this, we have made it clear that any\npatent must be licensed for everyone's free use or not licensed at all.\n\n The precise terms and conditions for copying, distribution and\nmodification follow.\n\n GNU GENERAL PUBLIC LICENSE\n TERMS AND CONDITIONS FOR COPYING, DISTRIBUTION AND MODIFICATION\n\n 0. This License applies to any program or other work which contains\na notice placed by the copyright holder saying it may be distributed\nunder the terms of this General Public License. The \"Program\", below,\nrefers to any such program or work, and a \"work based on the Program\"\nmeans either the Program or any derivative work under copyright law:\nthat is to say, a work containing the Program or a portion of it,\neither verbatim or with modifications and/or translated into another\nlanguage. (Hereinafter, translation is included without limitation in\nthe term \"modification\".) Each licensee is addressed as \"you\".\n\nActivities other than copying, distribution and modification are not\ncovered by this License; they are outside its scope. The act of\nrunning the Program is not restricted, and the output from the Program\nis covered only if its contents constitute a work based on the\nProgram (independent of having been made by running the Program).\nWhether that is true depends on what the Program does.\n\n 1. You may copy and distribute verbatim copies of the Program's\nsource code as you receive it, in any medium, provided that you\nconspicuously and appropriately publish on each copy an appropriate\ncopyright notice and disclaimer of warranty; keep intact all the\nnotices that refer to this License and to the absence of any warranty;\nand give any other recipients of the Program a copy of this License\nalong with the Program.\n\nYou may charge a fee for the physical act of transferring a copy, and\nyou may at your option offer warranty protection in exchange for a fee.\n\n 2. You may modify your copy or copies of the Program or any portion\nof it, thus forming a work based on the Program, and copy and\ndistribute such modifications or work under the terms of Section 1\nabove, provided that you also meet all of these conditions:\n\n a) You must cause the modified files to carry prominent notices\n stating that you changed the files and the date of any change.\n\n b) You must cause any work that you distribute or publish, that in\n whole or in part contains or is derived from the Program or any\n part thereof, to be licensed as a whole at no charge to all third\n parties under the terms of this License.\n\n c) If the modified program normally reads commands interactively\n when run, you must cause it, when started running for such\n interactive use in the most ordinary way, to print or display an\n announcement including an appropriate copyright notice and a\n notice that there is no warranty (or else, saying that you provide\n a warranty) and that users may redistribute the program under\n these conditions, and telling the user how to view a copy of this\n License. (Exception: if the Program itself is interactive but\n does not normally print such an announcement, your work based on\n the Program is not required to print an announcement.)\n\nThese requirements apply to the modified work as a whole. If\nidentifiable sections of that work are not derived from the Program,\nand can be reasonably considered independent and separate works in\nthemselves, then this License, and its terms, do not apply to those\nsections when you distribute them as separate works. But when you\ndistribute the same sections as part of a whole which is a work based\non the Program, the distribution of the whole must be on the terms of\nthis License, whose permissions for other licensees extend to the\nentire whole, and thus to each and every part regardless of who wrote it.\n\nThus, it is not the intent of this section to claim rights or contest\nyour rights to work written entirely by you; rather, the intent is to\nexercise the right to control the distribution of derivative or\ncollective works based on the Program.\n\nIn addition, mere aggregation of another work not based on the Program\nwith the Program (or with a work based on the Program) on a volume of\na storage or distribution medium does not bring the other work under\nthe scope of this License.\n\n 3. You may copy and distribute the Program (or a work based on it,\nunder Section 2) in object code or executable form under the terms of\nSections 1 and 2 above provided that you also do one of the following:\n\n a) Accompany it with the complete corresponding machine-readable\n source code, which must be distributed under the terms of Sections\n 1 and 2 above on a medium customarily used for software interchange; or,\n\n b) Accompany it with a written offer, valid for at least three\n years, to give any third party, for a charge no more than your\n cost of physically performing source distribution, a complete\n machine-readable copy of the corresponding source code, to be\n distributed under the terms of Sections 1 and 2 above on a medium\n customarily used for software interchange; or,\n\n c) Accompany it with the information you received as to the offer\n to distribute corresponding source code. (This alternative is\n allowed only for noncommercial distribution and only if you\n received the program in object code or executable form with such\n an offer, in accord with Subsection b above.)\n\nThe source code for a work means the preferred form of the work for\nmaking modifications to it. For an executable work, complete source\ncode means all the source code for all modules it contains, plus any\nassociated interface definition files, plus the scripts used to\ncontrol compilation and installation of the executable. However, as a\nspecial exception, the source code distributed need not include\nanything that is normally distributed (in either source or binary\nform) with the major components (compiler, kernel, and so on) of the\noperating system on which the executable runs, unless that component\nitself accompanies the executable.\n\nIf distribution of executable or object code is made by offering\naccess to copy from a designated place, then offering equivalent\naccess to copy the source code from the same place counts as\ndistribution of the source code, even though third parties are not\ncompelled to copy the source along with the object code.\n\n 4. You may not copy, modify, sublicense, or distribute the Program\nexcept as expressly provided under this License. Any attempt\notherwise to copy, modify, sublicense or distribute the Program is\nvoid, and will automatically terminate your rights under this License.\nHowever, parties who have received copies, or rights, from you under\nthis License will not have their licenses terminated so long as such\nparties remain in full compliance.\n\n 5. You are not required to accept this License, since you have not\nsigned it. However, nothing else grants you permission to modify or\ndistribute the Program or its derivative works. These actions are\nprohibited by law if you do not accept this License. Therefore, by\nmodifying or distributing the Program (or any work based on the\nProgram), you indicate your acceptance of this License to do so, and\nall its terms and conditions for copying, distributing or modifying\nthe Program or works based on it.\n\n 6. Each time you redistribute the Program (or any work based on the\nProgram), the recipient automatically receives a license from the\noriginal licensor to copy, distribute or modify the Program subject to\nthese terms and conditions. You may not impose any further\nrestrictions on the recipients' exercise of the rights granted herein.\nYou are not responsible for enforcing compliance by third parties to\nthis License.\n\n 7. If, as a consequence of a court judgment or allegation of patent\ninfringement or for any other reason (not limited to patent issues),\nconditions are imposed on you (whether by court order, agreement or\notherwise) that contradict the conditions of this License, they do not\nexcuse you from the conditions of this License. If you cannot\ndistribute so as to satisfy simultaneously your obligations under this\nLicense and any other pertinent obligations, then as a consequence you\nmay not distribute the Program at all. For example, if a patent\nlicense would not permit royalty-free redistribution of the Program by\nall those who receive copies directly or indirectly through you, then\nthe only way you could satisfy both it and this License would be to\nrefrain entirely from distribution of the Program.\n\nIf any portion of this section is held invalid or unenforceable under\nany particular circumstance, the balance of the section is intended to\napply and the section as a whole is intended to apply in other\ncircumstances.\n\nIt is not the purpose of this section to induce you to infringe any\npatents or other property right claims or to contest validity of any\nsuch claims; this section has the sole purpose of protecting the\nintegrity of the free software distribution system, which is\nimplemented by public license practices. Many people have made\ngenerous contributions to the wide range of software distributed\nthrough that system in reliance on consistent application of that\nsystem; it is up to the author/donor to decide if he or she is willing\nto distribute software through any other system and a licensee cannot\nimpose that choice.\n\nThis section is intended to make thoroughly clear what is believed to\nbe a consequence of the rest of this License.\n\n 8. If the distribution and/or use of the Program is restricted in\ncertain countries either by patents or by copyrighted interfaces, the\noriginal copyright holder who places the Program under this License\nmay add an explicit geographical distribution limitation excluding\nthose countries, so that distribution is permitted only in or among\ncountries not thus excluded. In such case, this License incorporates\nthe limitation as if written in the body of this License.\n\n 9. The Free Software Foundation may publish revised and/or new versions\nof the General Public License from time to time. Such new versions will\nbe similar in spirit to the present version, but may differ in detail to\naddress new problems or concerns.\n\nEach version is given a distinguishing version number. If the Program\nspecifies a version number of this License which applies to it and \"any\nlater version\", you have the option of following the terms and conditions\neither of that version or of any later version published by the Free\nSoftware Foundation. If the Program does not specify a version number of\nthis License, you may choose any version ever published by the Free Software\nFoundation.\n\n 10. If you wish to incorporate parts of the Program into other free\nprograms whose distribution conditions are different, write to the author\nto ask for permission. For software which is copyrighted by the Free\nSoftware Foundation, write to the Free Software Foundation; we sometimes\nmake exceptions for this. Our decision will be guided by the two goals\nof preserving the free status of all derivatives of our free software and\nof promoting the sharing and reuse of software generally.\n\n NO WARRANTY\n\n 11. BECAUSE THE PROGRAM IS LICENSED FREE OF CHARGE, THERE IS NO WARRANTY\nFOR THE PROGRAM, TO THE EXTENT PERMITTED BY APPLICABLE LAW. EXCEPT WHEN\nOTHERWISE STATED IN WRITING THE COPYRIGHT HOLDERS AND/OR OTHER PARTIES\nPROVIDE THE PROGRAM \"AS IS\" WITHOUT WARRANTY OF ANY KIND, EITHER EXPRESSED\nOR IMPLIED, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF\nMERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE. THE ENTIRE RISK AS\nTO THE QUALITY AND PERFORMANCE OF THE PROGRAM IS WITH YOU. SHOULD THE\nPROGRAM PROVE DEFECTIVE, YOU ASSUME THE COST OF ALL NECESSARY SERVICING,\nREPAIR OR CORRECTION.\n\n 12. IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR AGREED TO IN WRITING\nWILL ANY COPYRIGHT HOLDER, OR ANY OTHER PARTY WHO MAY MODIFY AND/OR\nREDISTRIBUTE THE PROGRAM AS PERMITTED ABOVE, BE LIABLE TO YOU FOR DAMAGES,\nINCLUDING ANY GENERAL, SPECIAL, INCIDENTAL OR CONSEQUENTIAL DAMAGES ARISING\nOUT OF THE USE OR INABILITY TO USE THE PROGRAM (INCLUDING BUT NOT LIMITED\nTO LOSS OF DATA OR DATA BEING RENDERED INACCURATE OR LOSSES SUSTAINED BY\nYOU OR THIRD PARTIES OR A FAILURE OF THE PROGRAM TO OPERATE WITH ANY OTHER\nPROGRAMS), EVEN IF SUCH HOLDER OR OTHER PARTY HAS BEEN ADVISED OF THE\nPOSSIBILITY OF SUCH DAMAGES.\n\n END OF TERMS AND CONDITIONS\n\n How to Apply These Terms to Your New Programs\n\n If you develop a new program, and you want it to be of the greatest\npossible use to the public, the best way to achieve this is to make it\nfree software which everyone can redistribute and change under these terms.\n\n To do so, attach the following notices to the program. It is safest\nto attach them to the start of each source file to most effectively\nconvey the exclusion of warranty; and each file should have at least\nthe \"copyright\" line and a pointer to where the full notice is found.\n\n <one line to give the program's name and a brief idea of what it does.>\n Copyright (C) <year> <name of author>\n\n This program is free software; you can redistribute it and/or modify\n it under the terms of the GNU General Public License as published by\n the Free Software Foundation; either version 2 of the License, or\n (at your option) any later version.\n\n This program is distributed in the hope that it will be useful,\n but WITHOUT ANY WARRANTY; without even the implied warranty of\n MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the\n GNU General Public License for more details.\n\n You should have received a copy of the GNU General Public License along\n with this program; if not, write to the Free Software Foundation, Inc.,\n 51 Franklin Street, Fifth Floor, Boston, MA 02110-1301 USA.\n\nAlso add information on how to contact you by electronic and paper mail.\n\nIf the program is interactive, make it output a short notice like this\nwhen it starts in an interactive mode:\n\n Gnomovision version 69, Copyright (C) year name of author\n Gnomovision comes with ABSOLUTELY NO WARRANTY; for details type `show w'.\n This is free software, and you are welcome to redistribute it\n under certain conditions; type `show c' for details.\n\nThe hypothetical commands `show w' and `show c' should show the appropriate\nparts of the General Public License. Of course, the commands you use may\nbe called something other than `show w' and `show c'; they could even be\nmouse-clicks or menu items--whatever suits your program.\n\nYou should also get your employer (if you work as a programmer) or your\nschool, if any, to sign a \"copyright disclaimer\" for the program, if\nnecessary. Here is a sample; alter the names:\n\n Yoyodyne, Inc., hereby disclaims all copyright interest in the program\n `Gnomovision' (which makes passes at compilers) written by James Hacker.\n\n <signature of Ty Coon>, 1 April 1989\n Ty Coon, President of Vice\n\nThis General Public License does not permit incorporating your program into\nproprietary programs. If your program is a subroutine library, you may\nconsider it more useful to permit linking proprietary applications with the\nlibrary. If this is what you want to do, use the GNU Lesser General\nPublic License instead of this License.\n",
"summary": "Network Automation from the Command Line",
"version": "1.8.3",
"project_urls": null,
"split_keywords": [
"networking",
" automation",
" typer",
" cli",
" python"
],
"urls": [
{
"comment_text": "",
"digests": {
"blake2b_256": "6206342388a74e4e14bf37c08b7d6dbad99c25f0e54be13b4ca9a1d8d3b1131d",
"md5": "4b8fd18371aa3e794394ffdf5658689d",
"sha256": "26441cc4dcab58aa99f37daa388b37b63d587a079e513f7704f4a7ca4b2b5ed8"
},
"downloads": -1,
"filename": "cli_automation-1.8.3-py3-none-any.whl",
"has_sig": false,
"md5_digest": "4b8fd18371aa3e794394ffdf5658689d",
"packagetype": "bdist_wheel",
"python_version": "py3",
"requires_python": "<4.0,>=3.10",
"size": 237163,
"upload_time": "2025-10-27T03:12:29",
"upload_time_iso_8601": "2025-10-27T03:12:29.829928Z",
"url": "https://files.pythonhosted.org/packages/62/06/342388a74e4e14bf37c08b7d6dbad99c25f0e54be13b4ca9a1d8d3b1131d/cli_automation-1.8.3-py3-none-any.whl",
"yanked": false,
"yanked_reason": null
},
{
"comment_text": "",
"digests": {
"blake2b_256": "a96986c7820d7e96494e0af23e3df57b9801833f313e4947dd4fddaaa2da933a",
"md5": "36b051db1450d5416e58993fdd404074",
"sha256": "8abf8f03b477cc1356810e98c2b9b4592ec81a81d3e6eaedd8de292f2bd16ab0"
},
"downloads": -1,
"filename": "cli_automation-1.8.3.tar.gz",
"has_sig": false,
"md5_digest": "36b051db1450d5416e58993fdd404074",
"packagetype": "sdist",
"python_version": "source",
"requires_python": "<4.0,>=3.10",
"size": 233065,
"upload_time": "2025-10-27T03:12:31",
"upload_time_iso_8601": "2025-10-27T03:12:31.688206Z",
"url": "https://files.pythonhosted.org/packages/a9/69/86c7820d7e96494e0af23e3df57b9801833f313e4947dd4fddaaa2da933a/cli_automation-1.8.3.tar.gz",
"yanked": false,
"yanked_reason": null
}
],
"upload_time": "2025-10-27 03:12:31",
"github": false,
"gitlab": false,
"bitbucket": false,
"codeberg": false,
"lcname": "cli-automation"
}