<div align="center">
# p4lantir




</div>
***
**p4lantir** is a simple tool to perform Man-in-the-Middle over TCP using ARP spoofing, allowing to intercept, drop, forward and see TCP flows.
This project is intended to be relatively simple, making simple future contributions for new features/bug fix.
> [!CAUTION]
> This ethical hacking project is intended for educational purposes and awareness training sessions only. I decline all responsability about the usage of this project.
***
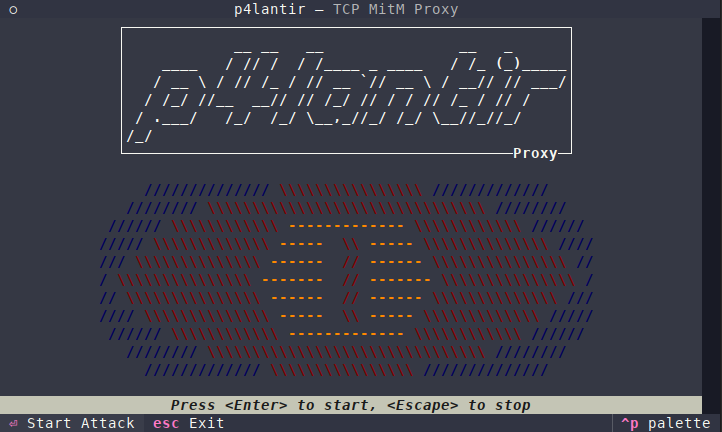
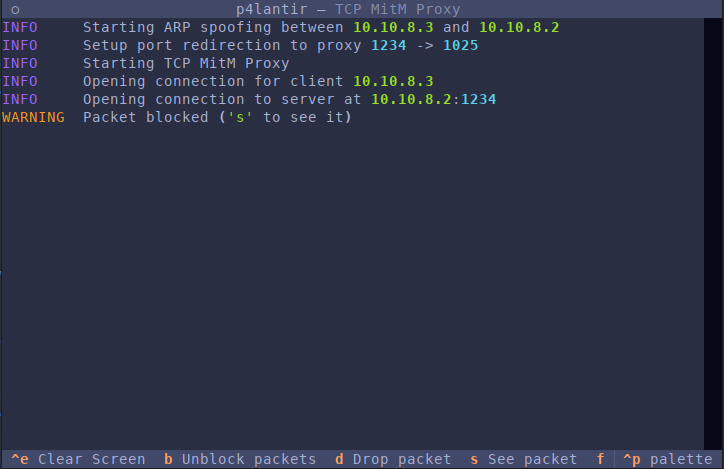
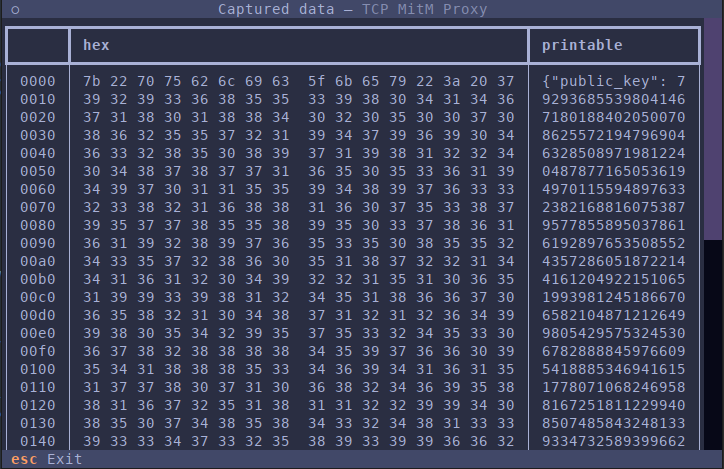
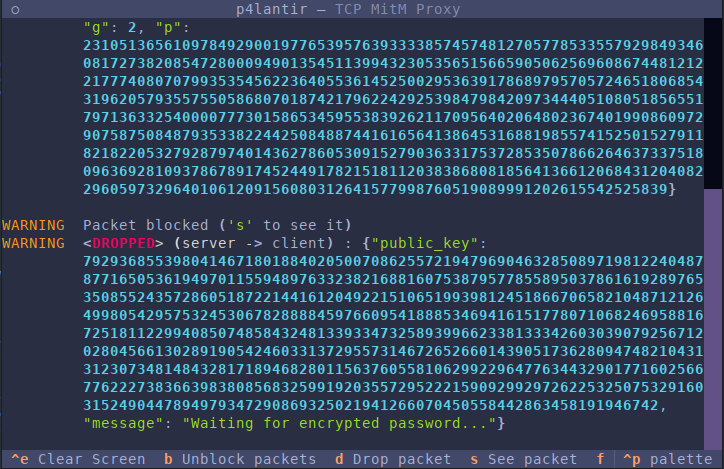
## Screenshots
## Installation
- Install the system dependencies (arpspoof, iptables)
- Create python virtual environnement
- Install the package
Setup instructions :
- [Debian-based (Debian, Kali, Ubuntu,...)](#debian-based-systems)
- [Archlinux](#archlinux)
### Debian-based systems
```bash
sudo apt install dsniff iptables
python3 -m venv venv
source venv/bin/activate
pip install p4lantir
```
### Archlinux
```bash
pacman -S dsniff iptables
python3 -m venv venv
source venv/bin/activate
pip install p4lantir
```
> Note : the package can also be downloaded from the release and installed using the `.whl` file and `pip`.
## Usage
> [!WARNING]
> You need to run the script as root due to arpspoof and iptables. You should open a shell as root, activate the venv and then use *p4lantir*.
```
usage: p4lantir [-h] --host-1 HOST_1 --host-2 HOST_2 [--gateway GATEWAY] -i INTERFACE -l LPORT [--pport PPORT] [--debug]
Man-in-the-Middle over TCP terminal app.
options:
-h, --help show this help message and exit
--host-1 HOST_1 First host to spoof, must be the host instanciating the connection
--host-2 HOST_2 Second host to spoof
--gateway GATEWAY Gateway IP
-i, --interface INTERFACE
Interface to perform arp spoofing
-l, --lport LPORT Port to listen for MITM attack
--pport PPORT Internal port used for proxy.
--debug Enable debug mode.
```
### Examples
#### Client/server in the same localhost
Let say that a client at IP *C* connect to a remote server at IP *R*, both in the same LAN. You need to know the name of the interface that connects you this LAN (let call this *iface*. Then your command should look like :
```bash
p4lantir --host-1 [replace with C] \
--host-2 [replace with R] \
-i [replace with iface] \
-lport [server's listening port]
```
> About the listening port, if you intend to intercept SMTP you may choose `25`, `80` for HTTP, and so on ...
### Client/server on a different LAN
If the client is in the same LAN as you and the server is not in your LAN, then you have to add another parameter : the gateway IP. *p4lantir* will then spoof the gateway IP and open a connection to the server.
```bash
p4lantir --host-1 [replace with C] \
--host-2 [replace with R] \
--gateway [replace with gw's IP]
-i [replace with iface] \
-lport [server's listening port]
```
## Documentation
The source-code documentation is available [here](https://www.acmo0.org/p4lantir/)
## Contributing
**All contributions are welcome !**
Please see [CONTRIBUTING.md](./CONTRIBUTING.md) for more details.
## License
This project is under the GPL-v3 license, please see [LICENSE.TXT](./LICENSE.TXT)
Raw data
{
"_id": null,
"home_page": null,
"name": "p4lantir",
"maintainer": null,
"docs_url": null,
"requires_python": ">=3.9",
"maintainer_email": null,
"keywords": "TCP, man-in-the-middle, mitm, proxy, textual",
"author": "acmo0",
"author_email": null,
"download_url": "https://files.pythonhosted.org/packages/7d/79/500149476dc7ac80d1907dca1ed6e8e09fc647effe6b392c24259211ffe6/p4lantir-1.0.2.tar.gz",
"platform": null,
"description": "<div align=\"center\">\n\n# p4lantir\n\n\n\n\n\n\n\n\n</div>\n\n***\n\n**p4lantir** is a simple tool to perform Man-in-the-Middle over TCP using ARP spoofing, allowing to intercept, drop, forward and see TCP flows.\n\nThis project is intended to be relatively simple, making simple future contributions for new features/bug fix.\n\n> [!CAUTION]\n> This ethical hacking project is intended for educational purposes and awareness training sessions only. I decline all responsability about the usage of this project.\n\n***\n\n## Screenshots\n\n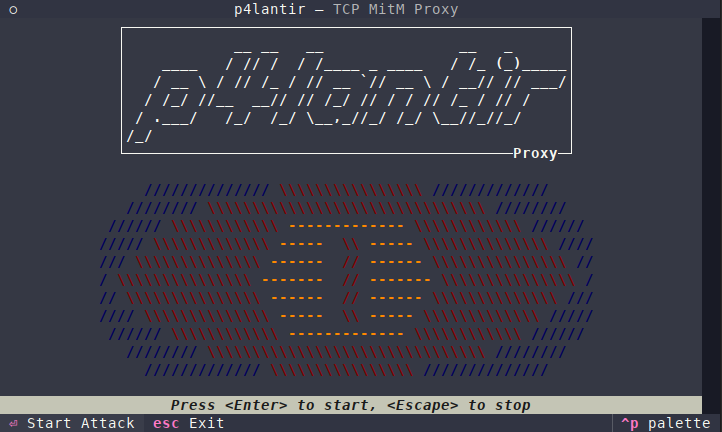\n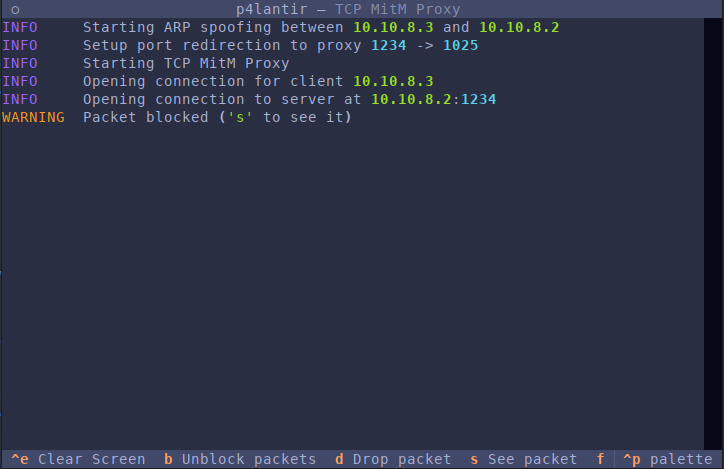\n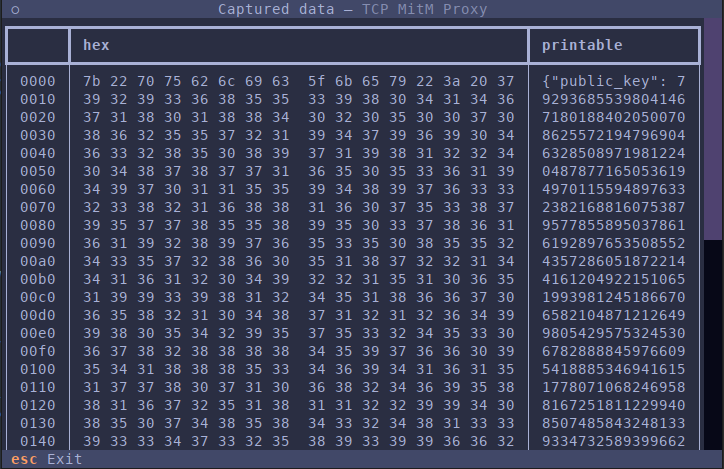\n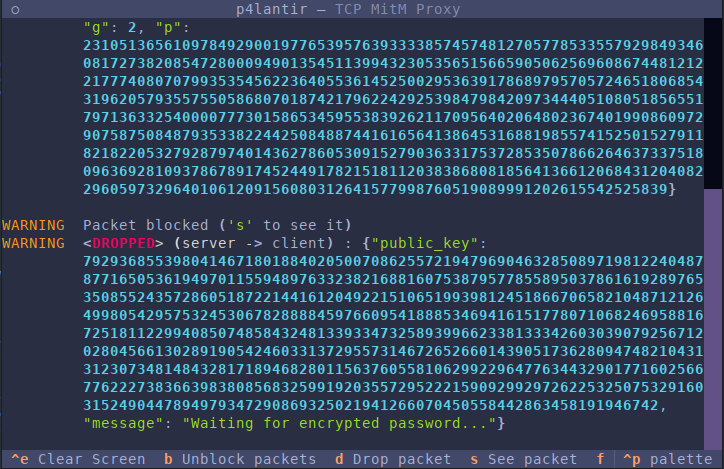\n\n\n## Installation\n- Install the system dependencies (arpspoof, iptables)\n- Create python virtual environnement\n- Install the package\n\nSetup instructions :\n- [Debian-based (Debian, Kali, Ubuntu,...)](#debian-based-systems)\n- [Archlinux](#archlinux)\n\n### Debian-based systems\n```bash\nsudo apt install dsniff iptables\n\npython3 -m venv venv\nsource venv/bin/activate\n\npip install p4lantir\n```\n\n### Archlinux\n```bash\npacman -S dsniff iptables\n\npython3 -m venv venv\nsource venv/bin/activate\n\npip install p4lantir\n```\n\n> Note : the package can also be downloaded from the release and installed using the `.whl` file and `pip`.\n\n## Usage\n> [!WARNING]\n> You need to run the script as root due to arpspoof and iptables. You should open a shell as root, activate the venv and then use *p4lantir*.\n```\nusage: p4lantir [-h] --host-1 HOST_1 --host-2 HOST_2 [--gateway GATEWAY] -i INTERFACE -l LPORT [--pport PPORT] [--debug]\n\nMan-in-the-Middle over TCP terminal app.\n\noptions:\n -h, --help show this help message and exit\n --host-1 HOST_1 First host to spoof, must be the host instanciating the connection\n --host-2 HOST_2 Second host to spoof\n --gateway GATEWAY Gateway IP\n -i, --interface INTERFACE\n Interface to perform arp spoofing\n -l, --lport LPORT Port to listen for MITM attack\n --pport PPORT Internal port used for proxy.\n --debug Enable debug mode.\n```\n\n### Examples\n#### Client/server in the same localhost\n\nLet say that a client at IP *C* connect to a remote server at IP *R*, both in the same LAN. You need to know the name of the interface that connects you this LAN (let call this *iface*. Then your command should look like :\n```bash\np4lantir --host-1 [replace with C] \\\n --host-2 [replace with R] \\\n -i [replace with iface] \\\n -lport [server's listening port]\n```\n\n> About the listening port, if you intend to intercept SMTP you may choose `25`, `80` for HTTP, and so on ...\n\n### Client/server on a different LAN\n\nIf the client is in the same LAN as you and the server is not in your LAN, then you have to add another parameter : the gateway IP. *p4lantir* will then spoof the gateway IP and open a connection to the server.\n```bash\np4lantir --host-1 [replace with C] \\\n --host-2 [replace with R] \\\n --gateway [replace with gw's IP]\n -i [replace with iface] \\\n -lport [server's listening port]\n```\n\n## Documentation\nThe source-code documentation is available [here](https://www.acmo0.org/p4lantir/)\n\n\n## Contributing\n**All contributions are welcome !**\n\nPlease see [CONTRIBUTING.md](./CONTRIBUTING.md) for more details.\n\n## License\nThis project is under the GPL-v3 license, please see [LICENSE.TXT](./LICENSE.TXT)\n",
"bugtrack_url": null,
"license": null,
"summary": "MiTM over TCP to intercept and manipulate flow",
"version": "1.0.2",
"project_urls": {
"Repository": "https://github.com/acmo0/p4lantir.git"
},
"split_keywords": [
"tcp",
" man-in-the-middle",
" mitm",
" proxy",
" textual"
],
"urls": [
{
"comment_text": null,
"digests": {
"blake2b_256": "33e921ebfb0ea26c685ca465e59a1fc135de4301b89b3b75f4d65543d94f6028",
"md5": "51416cdfb63a44674fa34cca60f890bb",
"sha256": "91dc07eac206321b2ea3b71a2f743d6dadcb55c7f96f3f5051dad947a7303ffd"
},
"downloads": -1,
"filename": "p4lantir-1.0.2-py3-none-any.whl",
"has_sig": false,
"md5_digest": "51416cdfb63a44674fa34cca60f890bb",
"packagetype": "bdist_wheel",
"python_version": "py3",
"requires_python": ">=3.9",
"size": 26938,
"upload_time": "2025-08-26T07:32:13",
"upload_time_iso_8601": "2025-08-26T07:32:13.656602Z",
"url": "https://files.pythonhosted.org/packages/33/e9/21ebfb0ea26c685ca465e59a1fc135de4301b89b3b75f4d65543d94f6028/p4lantir-1.0.2-py3-none-any.whl",
"yanked": false,
"yanked_reason": null
},
{
"comment_text": null,
"digests": {
"blake2b_256": "7d79500149476dc7ac80d1907dca1ed6e8e09fc647effe6b392c24259211ffe6",
"md5": "820fb8502668bf67c562cae94633b43d",
"sha256": "453326e910a977daf80b0eadb8b18f9534c3c5f2e90f41ddd23b977066a1ff31"
},
"downloads": -1,
"filename": "p4lantir-1.0.2.tar.gz",
"has_sig": false,
"md5_digest": "820fb8502668bf67c562cae94633b43d",
"packagetype": "sdist",
"python_version": "source",
"requires_python": ">=3.9",
"size": 337622,
"upload_time": "2025-08-26T07:32:15",
"upload_time_iso_8601": "2025-08-26T07:32:15.060783Z",
"url": "https://files.pythonhosted.org/packages/7d/79/500149476dc7ac80d1907dca1ed6e8e09fc647effe6b392c24259211ffe6/p4lantir-1.0.2.tar.gz",
"yanked": false,
"yanked_reason": null
}
],
"upload_time": "2025-08-26 07:32:15",
"github": true,
"gitlab": false,
"bitbucket": false,
"codeberg": false,
"github_user": "acmo0",
"github_project": "p4lantir",
"travis_ci": false,
"coveralls": false,
"github_actions": true,
"requirements": [
{
"name": "astroid",
"specs": [
[
"==",
"3.3.11"
]
]
},
{
"name": "colorlog",
"specs": [
[
"==",
"6.9.0"
]
]
},
{
"name": "dill",
"specs": [
[
"==",
"0.4.0"
]
]
},
{
"name": "isort",
"specs": [
[
"==",
"6.0.1"
]
]
},
{
"name": "linkify-it-py",
"specs": [
[
"==",
"2.0.3"
]
]
},
{
"name": "markdown-it-py",
"specs": [
[
"==",
"4.0.0"
]
]
},
{
"name": "mccabe",
"specs": [
[
"==",
"0.7.0"
]
]
},
{
"name": "mdit-py-plugins",
"specs": [
[
"==",
"0.5.0"
]
]
},
{
"name": "mdurl",
"specs": [
[
"==",
"0.1.2"
]
]
},
{
"name": "platformdirs",
"specs": [
[
"==",
"4.3.8"
]
]
},
{
"name": "Pygments",
"specs": [
[
"==",
"2.19.2"
]
]
},
{
"name": "rich",
"specs": [
[
"==",
"14.1.0"
]
]
},
{
"name": "textual",
"specs": [
[
"==",
"5.3.0"
]
]
},
{
"name": "tomlkit",
"specs": [
[
"==",
"0.13.3"
]
]
},
{
"name": "typing_extensions",
"specs": [
[
"==",
"4.14.1"
]
]
},
{
"name": "uc-micro-py",
"specs": [
[
"==",
"1.0.3"
]
]
},
{
"name": "uv",
"specs": [
[
"==",
"0.8.13"
]
]
}
],
"lcname": "p4lantir"
}
